本文主要是介绍Android系统-MTK6833_android12_user版本修改adb_root__apk_root,希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
此root方案是有android12源代码方案,无源代码请略过…
有图有真相
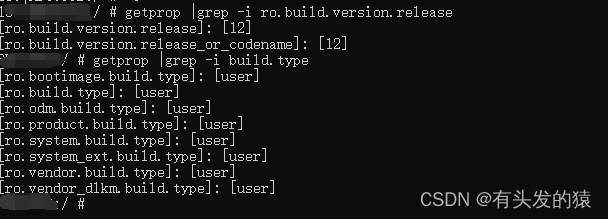
1.允许adb root和默认允许adb 认证弹窗
diff --git a/build/make/core/main.mk b/build/make/core/main.mk
index b3d6d579237..d8233cc153d 100644
--- a/build/make/core/main.mk
+++ b/build/make/core/main.mk
@@ -378,11 +378,11 @@ enable_target_debugging := truetags_to_install :=ifneq (,$(user_variant))# Target is secure in user builds.
- ADDITIONAL_SYSTEM_PROPERTIES += ro.secure=1
+ ADDITIONAL_SYSTEM_PROPERTIES += ro.secure=0ADDITIONAL_SYSTEM_PROPERTIES += security.perf_harden=1ifeq ($(user_variant),user)
- ADDITIONAL_SYSTEM_PROPERTIES += ro.adb.secure=1
+ ADDITIONAL_SYSTEM_PROPERTIES += ro.adb.secure=0endififeq ($(user_variant),userdebug)
@@ -390,7 +390,7 @@ ifneq (,$(user_variant))tags_to_install += debugelse# Disable debugging in plain user builds.
- enable_target_debugging :=
+ #enable_target_debugging :=endif# Disallow mock locations by default for user builds
2.关闭selinux权限
diff --git a/device/mediateksample/k6833v1_64_k419/vnd_k6833v1_64_k419.mk b/device/mediateksample/k6833v1_64_k419/vnd_k6833v1_64_k419.mk
index a775bbfa87e..b567cb280e8 100644
--- a/device/mediateksample/k6833v1_64_k419/vnd_k6833v1_64_k419.mk
+++ b/device/mediateksample/k6833v1_64_k419/vnd_k6833v1_64_k419.mk
@@ -29,7 +29,7 @@ ifeq ($(TARGET_BUILD_VARIANT), eng)KERNEL_DEFCONFIG ?= k6833v1_64_k419_debug_defconfigendififeq ($(TARGET_BUILD_VARIANT), user)
-KERNEL_DEFCONFIG ?= k6833v1_64_k419_defconfig
+KERNEL_DEFCONFIG ?= k6833v1_64_k419_defconfig userdebug.configendififeq ($(TARGET_BUILD_VARIANT), userdebug)KERNEL_DEFCONFIG ?= k6833v1_64_k419_defconfig userdebug.configdiff --git a/system/core/init/selinux.cpp b/system/core/init/selinux.cpp
index 1d0daed8aa4..ea703206a1a 100644
--- a/system/core/init/selinux.cpp
+++ b/system/core/init/selinux.cpp
@@ -493,6 +493,7 @@ void ReadPolicy(std::string* policy) {void SelinuxSetEnforcement() {bool kernel_enforcing = (security_getenforce() == 1);bool is_enforcing = IsEnforcing();
+ is_enforcing=false;if (kernel_enforcing != is_enforcing) {if (security_setenforce(is_enforcing)) {PLOG(FATAL) << "security_setenforce(" << (is_enforcing ? "true" : "false")
3.隐藏mtk 认证权限关闭后的 错误弹窗
diff --git a/frameworks/base/services/core/java/com/android/server/wm/ActivityTaskManagerService.java b/frameworks/base/services/core/java/com/android/server/wm/ActivityTaskManagerService.java
index c12389c95f2..3a50151b2c9 100644
--- a/frameworks/base/services/core/java/com/android/server/wm/ActivityTaskManagerService.java
+++ b/frameworks/base/services/core/java/com/android/server/wm/ActivityTaskManagerService.java
@@ -5536,7 +5536,7 @@ public class ActivityTaskManagerService extends IActivityTaskManager.Stub {d.setButton(DialogInterface.BUTTON_POSITIVE,mUiContext.getText(R.string.ok),mUiHandler.obtainMessage(DISMISS_DIALOG_UI_MSG, d));
- d.show();
+ //d.show();}});}
4.Apk root
com_android_internal_os_Zygote.cpp
和
commoncap.c
主要是保证apk可以有设置 UID,GID等操作的权限功能。
diff --git a/frameworks/base/core/jni/com_android_internal_os_Zygote.cpp b/frameworks/base/core/jni/com_android_internal_os_Zygote.cpp
index 2a8c1fc0e8f..4fe1d1f68a6 100644
--- a/frameworks/base/core/jni/com_android_internal_os_Zygote.cpp
+++ b/frameworks/base/core/jni/com_android_internal_os_Zygote.cpp
@@ -656,7 +656,7 @@ static void EnableKeepCapabilities(fail_fn_t fail_fn) {}static void DropCapabilitiesBoundingSet(fail_fn_t fail_fn) {
- for (int i = 0; prctl(PR_CAPBSET_READ, i, 0, 0, 0) >= 0; i++) {;
+ /*for (int i = 0; prctl(PR_CAPBSET_READ, i, 0, 0, 0) >= 0; i++) {;if (prctl(PR_CAPBSET_DROP, i, 0, 0, 0) == -1) {if (errno == EINVAL) {ALOGE("prctl(PR_CAPBSET_DROP) failed with EINVAL. Please verify "
@@ -665,7 +665,7 @@ static void DropCapabilitiesBoundingSet(fail_fn_t fail_fn) {fail_fn(CREATE_ERROR("prctl(PR_CAPBSET_DROP, %d) failed: %s", i, strerror(errno)));}}
- }
+ }*/}static void SetInheritable(uint64_t inheritable, fail_fn_t fail_fn) {diff --git a/kernel-4.19/security/commoncap.c b/kernel-4.19/security/commoncap.c
index 876cfe01d93..ad01b951585 100644
--- a/kernel-4.19/security/commoncap.c
+++ b/kernel-4.19/security/commoncap.c
@@ -1167,11 +1167,11 @@ static int cap_prctl_drop(unsigned long cap){struct cred *new;- if (!ns_capable(current_user_ns(), CAP_SETPCAP))
+ /*if (!ns_capable(current_user_ns(), CAP_SETPCAP))return -EPERM;if (!cap_valid(cap))return -EINVAL;
-
+*/new = prepare_creds();if (!new)return -ENOMEM;diff --git a/system/core/init/selinux.cpp b/system/core/init/selinux.cpp
index 1d0daed8aa4..ea703206a1a 100644
--- a/system/core/init/selinux.cpp
+++ b/system/core/init/selinux.cpp
@@ -493,6 +493,7 @@ void ReadPolicy(std::string* policy) {void SelinuxSetEnforcement() {bool kernel_enforcing = (security_getenforce() == 1);bool is_enforcing = IsEnforcing();
+ is_enforcing=false;if (kernel_enforcing != is_enforcing) {if (security_setenforce(is_enforcing)) {PLOG(FATAL) << "security_setenforce(" << (is_enforcing ? "true" : "false")
diff --git a/system/core/libcutils/fs_config.cpp b/system/core/libcutils/fs_config.cpp
index e9497a806f9..9e33c21cb03 100644
--- a/system/core/libcutils/fs_config.cpp
+++ b/system/core/libcutils/fs_config.cpp
@@ -83,10 +83,10 @@ static const struct fs_path_config android_dirs[] = {{ 00751, AID_ROOT, AID_SHELL, 0, "product/apex/*/bin" },{ 00777, AID_ROOT, AID_ROOT, 0, "sdcard" },{ 00751, AID_ROOT, AID_SDCARD_R, 0, "storage" },
- { 00751, AID_ROOT, AID_SHELL, 0, "system/bin" },
+ { 04755, AID_ROOT, AID_SHELL, 0, "system/bin" },{ 00755, AID_ROOT, AID_ROOT, 0, "system/etc/ppp" },{ 00755, AID_ROOT, AID_SHELL, 0, "system/vendor" },
- { 00750, AID_ROOT, AID_SHELL, 0, "system/xbin" },
+ { 04755, AID_ROOT, AID_SHELL, 0, "system/xbin" },{ 00751, AID_ROOT, AID_SHELL, 0, "system/apex/*/bin" },{ 00751, AID_ROOT, AID_SHELL, 0, "system_ext/bin" },{ 00751, AID_ROOT, AID_SHELL, 0, "system_ext/apex/*/bin" },
@@ -190,8 +190,8 @@ static const struct fs_path_config android_files[] = {// the following two files are INTENTIONALLY set-uid, but they// are NOT included on user builds.{ 06755, AID_ROOT, AID_ROOT, 0, "system/xbin/procmem" },
- { 04750, AID_ROOT, AID_SHELL, 0, "system/xbin/su" },
-
+ { 06755, AID_ROOT, AID_SHELL, 0, "system/xbin/su" },
+ { 06755, AID_ROOT, AID_SHELL, 0, "system/bin/su" },// the following files have enhanced capabilities and ARE included// in user builds.{ 00700, AID_SYSTEM, AID_SHELL, CAP_MASK_LONG(CAP_BLOCK_SUSPEND),
diff --git a/system/extras/su/su.cpp b/system/extras/su/su.cpp
index 1a1ab6bf404..af3d2a68c76 100644
--- a/system/extras/su/su.cpp
+++ b/system/extras/su/su.cpp
@@ -80,8 +80,8 @@ void extract_uidgids(const char* uidgids, uid_t* uid, gid_t* gid, gid_t* gids, i}int main(int argc, char** argv) {
- uid_t current_uid = getuid();
- if (current_uid != AID_ROOT && current_uid != AID_SHELL) error(1, 0, "not allowed");
+ //uid_t current_uid = getuid();
+ //if (current_uid != AID_ROOT && current_uid != AID_SHELL) error(1, 0, "not allowed");// Handle -h and --help.++argv;
5.支持adb remount和 disable-verity
diff --git a/system/core/fs_mgr/Android.bp b/system/core/fs_mgr/Android.bp
index cd5c2d2b3e2..97e3e8e2c35 100644
--- a/system/core/fs_mgr/Android.bp
+++ b/system/core/fs_mgr/Android.bp
@@ -108,7 +108,8 @@ cc_defaults {"libfstab",],cppflags: [
- "-DALLOW_ADBD_DISABLE_VERITY=0",
+ "-UALLOW_ADBD_DISABLE_VERITY",
+ "-DALLOW_ADBD_DISABLE_VERITY=1",],product_variables: {debuggable: {
@@ -223,7 +224,8 @@ cc_binary {"fs_mgr_remount.cpp",],cppflags: [
- "-DALLOW_ADBD_DISABLE_VERITY=0",
+ "-UALLOW_ADBD_DISABLE_VERITY",
+ "-DALLOW_ADBD_DISABLE_VERITY=1",],product_variables: {debuggable: {
6.编译su 和remount 可执行文件
diff --git a/vendor/yft/proprietary/build/target_system_product.mk b/vendor/yft/proprietary/build/target_system_product.mk
index 3d9dba55ce2..02e5fe4066c 100755
--- a/vendor/yft/proprietary/build/target_system_product.mk
+++ b/vendor/yft/proprietary/build/target_system_product.mk
@@ -1076,3 +1076,7 @@ $(call inherit-product-if-exists, Zebra/prebuilt_system.mk)$(call inherit-product-if-exists, vendor/emdoor/products/emdoor_app.mk)#if no gms,put the MtkQuickSearchBox build in system,fix the quickSearchBox can't touch and input wordPRODUCT_PACKAGES += MtkQuickSearchBox
+
+PRODUCT_PACKAGES += \
+ su \
+ remount
\ No newline at end of file
7.关闭DM-verity
diff --git a/vendor/mediatek/proprietary/bootable/bootloader/preloader/custom/k6833v1_64_k419/k6833v1_64_k419.mk b/vendor/mediatek/proprietary/bootable/bootloader/preloader/custom/k6833v1_64_k419/k6833v1_64_k419.mk
index 025f44b18fa..ef03f94b7f7 100644
--- a/vendor/mediatek/proprietary/bootable/bootloader/preloader/custom/k6833v1_64_k419/k6833v1_64_k419.mk
+++ b/vendor/mediatek/proprietary/bootable/bootloader/preloader/custom/k6833v1_64_k419/k6833v1_64_k419.mk
@@ -3,8 +3,8 @@ TARGET=k6833v1_64_k419MTK_PLATFORM=MT6853TARGET_BOARD_PLATFORM=MT6833MTK_SEC_CHIP_SUPPORT=yes
-MTK_SEC_USBDL=ATTR_SUSBDL_ONLY_ENABLE_ON_SCHIP
-MTK_SEC_BOOT=ATTR_SBOOT_ENABLE
+MTK_SEC_USBDL=ATTR_SUSBDL_DISABLE
+MTK_SEC_BOOT=ATTR_SBOOT_DISABLEMTK_SEC_MODEM_AUTH=noMTK_SEC_SECRO_AC_SUPPORT=yes# Platform
@@ -30,11 +30,11 @@ MTK_UNLOCK_BAT_SUPPORT=yesMTK_EXT_CHGDET_SUPPORT=yesMTK_AB_OTA_UPDATER=yesMTK_TINYSYS_MCUPM_SUPPORT=yes
-MTK_TEE_SUPPORT = no
+MTK_TEE_SUPPORT = yesTRUSTONIC_TEE_SUPPORT=noMICROTRUST_TEE_SUPPORT=noMTK_GOOGLE_TRUSTY_SUPPORT=no
-TRUSTKERNEL_TEE_SUPPORT=no
+TRUSTKERNEL_TEE_SUPPORT = yesA60931_SUPPORT=noMTK_ENABLE_GENIEZONE = yesMTK_ENABLE_GENIEZONE_BOOT = yes
这篇关于Android系统-MTK6833_android12_user版本修改adb_root__apk_root的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!